Latest Version
3.2.43
September 12, 2024
VPN SATOSHI
Tools
Android
0
Free
com.satoshi.vpns
Report a Problem
More About VPN Satoshi
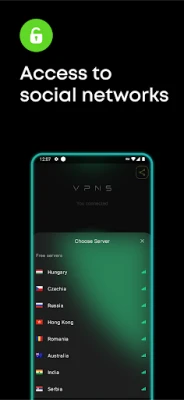
Maximizing Data Transfer Speed and Security in Network Connections
In today's digital landscape, ensuring efficient and secure data transfer is paramount. When a customer connects to a network, the system intelligently selects the nearest and least congested node. This strategic choice guarantees optimal data transfer speeds, enhancing the overall user experience.
Understanding Node Selection for Enhanced Performance
The process of connecting to a network involves sophisticated algorithms that assess various nodes. By automatically choosing the closest and least busy node, the system minimizes latency and maximizes throughput. This not only accelerates data transfer but also reduces the likelihood of connection drops, providing a seamless experience for users.
The Role of Encryption in Data Security
As data travels between the client and the selected node, it undergoes robust encryption using cutting-edge algorithms. This encryption process is crucial for safeguarding sensitive information from potential threats. By employing advanced security measures, the network ensures that all data remains confidential and protected against unauthorized access.
Benefits of Optimized Node Selection
- Improved Speed: By connecting to the nearest node, users experience faster data transfer rates, which is essential for activities such as streaming, gaming, and large file downloads.
- Reduced Latency: Selecting the least busy node minimizes delays, resulting in a more responsive connection that enhances real-time applications like video conferencing.
- Increased Reliability: A well-optimized network connection reduces the chances of interruptions, ensuring a stable and consistent user experience.
Advanced Encryption Techniques for Maximum Security
Data encryption is a critical component of modern network security. The use of state-of-the-art encryption algorithms ensures that all information exchanged between the client and the node is secure. These algorithms transform data into a format that is unreadable to anyone who does not possess the correct decryption key, thereby protecting it from cyber threats.
Types of Encryption Algorithms Used
Several encryption methods are commonly employed to secure data in transit:
- AES (Advanced Encryption Standard): Widely regarded as one of the most secure encryption methods, AES is used by governments and organizations worldwide to protect sensitive data.
- RSA (Rivest-Shamir-Adleman): This public-key encryption algorithm is essential for secure data transmission, particularly in establishing secure connections over the internet.
- SSL/TLS (Secure Sockets Layer/Transport Layer Security): These protocols encrypt data between web browsers and servers, ensuring secure online transactions and communications.
Conclusion: The Importance of Speed and Security in Network Connections
In conclusion, the intelligent selection of network nodes plays a vital role in optimizing data transfer speeds while maintaining high security standards. By leveraging advanced encryption techniques, networks can protect sensitive information and provide users with a reliable and efficient connection. As technology continues to evolve, the importance of both speed and security in network connections will only grow, making it essential for businesses and individuals alike to prioritize these factors in their digital interactions.
Rate the App
User Reviews
Popular Apps









Editor's Choice